| The Introduction to Computer Science I for non-majors by James Tam | Return to the course web page |
(Aside from storing the return value of certain string functions, lists should not be used in this assignment)
Encryption is the process of converting ordinary text into a form that cannot be read. Decryption is the reverse of encryption and takes unreadable encrypted information and restores the original message by reversing the original encryption algorithm. Encryption is an important part of computer security. Vast amounts of information are transmitted via the Internet and wireless networks each day and we've all heard stories of systems being 'hacked' and private information such credit and banking information being stolen. Encrypting data when it's transmitted or stored can increase security because all that will be seen of the encrypted text is gibberish. However there are good encryption algorithms and there are poor ones. Good encryption algorithms make it difficult or impossible to restore the original information. This is why for web browsers 128 bit encryption is superior to the older form that only uses 64 bits and for wireless networks why 'WPA' replaced 'WEP'.
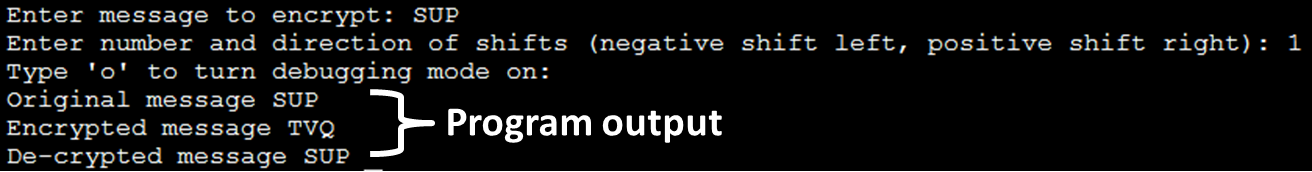
For this assignment you will write a program that will prompt the user for a string of alphabetic text, a number and whether the program will operate in 'debugging mode' or not (see Feature #4). The text will encrypted by shifting each character forward or backward in the alphabet depending on the size and sign of the number. A positive number shifts each character forward in the alphabet while a negative number shifts each character back.
Example: ABC, +2 (shift forward two)
A becomes C, B becomes D, C becomes E. Encrypted message = CDEExample: ABC, -1 (shift backward one)
A 'wraps' back to Z, B becomes A, C becomes B. Encrypted message = ZABExample: SUP? LOLZ, +1 (shift forward one)
S becomes T, U becomes V, P becomes Q, question mark unchanged, space unchanged, L becomes M, O becomes P, L becomes M, Z 'wraps' back to A
Shifting will only occur on capital letters. Lower case will be converted to upper case (you can use the upper() function [Example usage]) before shifting occurs. Shifts of 26 or greater simply results in some "wrap around" e.g. 'A' shifted forward 25 places becomes 'Z', while 'A' shifted forward 26 places is unchanged, 'A' shifted forward 27 places becomes 'B'. The only non-alphabetic characters allowed in the text include: punctuation (! . ?), commas (,), the apostrophe (') and the space character. The allowable non-alphabetic characters should not be encrypted. The presence of other non-alphabetic characters (e.g., a dollar sign) should result in the encryption process ending immediately at that point (decryption will not occur). Partial encryption may occur (see the figure below). Finally the program should be able to reverse the process by shifting each character in the opposite direction. The program should always display: the original text, the encrypted text and the decrypted text (which should match the original text). A debug mode will be used to quickly determine if encryption/decryption is correct (displays each character along with its corresponding ASCII code).
 |
 |
| Invalid character entered: debugging messages OFF | Invalid character entered: debugging messages ON |
|
|
|
|
|
|
 |
|
|
|
|
Character information before encryption/decryption: <ASCII code> <dash> <character> <tab> Character information after encryption/decryption: <ASCII code> <dash> <character>
The purpose of this feature is to make it SIGNIFICANTLY easier for you and your marker to determine if your program is working. (For your reference: You can look up the ASCII table at the UNIX command line by typing "man ascii" or you can use the Python ord() function). |
|
Finally you need to decompose your programs into functions and employ parameter passing and return values in your functions. The decomposition be logical and well balanced between functions. For example you shouldn't name a function 'decrypt' if it actually encrypts text. Nor should you write one or more 'super' functions where most/all of the program instructions reside and a few trivial functions that do almost nothing.
They can be found in the course directory under: /home/courses/217/assignments/assignment4